Trust is Overrated
trust but authenticate
A big story I soaked in as a MIDN and JO was what the damage the John Walker spy ring did to the US military. It took a decade and a bit higher clearance until I started to understand the depth of what he did.
His network followed a tradition going back to the start of our species; spying. Secrets are just part of warfare … as are steps to secure those secrets … and get around barriers. It is an ever evolving game.
At some point you have to trust your people and the security clearance process to get work done, but it helps to be a bit paranoid. Wars can be won or lost from spying. You do what you can to avoid compromise, but one thing you can’t do it actually know what is going on in the human mind. Humans are complicated and imperfect – and no security program will be air tight.
In a program that pre-dates the Massachusetts ANG Airman’s latest story, it appears we are going to pull the security ratchet harder.
Up to speed on “Zero Trust?” You need to be.
Navy CTO Don Yeske said April 26 during the virtual C4ISRNET Conference that while a zero-trust approach to network defense may not have prevented the leak, the underlying tenets would have helped the department detect the security breach sooner.
“The whole point of zero trust is to never trust. Always verify and assume breach,” Yeske said. “You begin from the point of assuming your network has been compromised, and if it hasn’t been compromised, that compromise is inevitable. Insider threats light up like a Christmas tree when that is your approach.”
The Pentagon released its zero-trust strategy last November, laying out a plan to implement the basic elements of the “trust no one” approach by 2027. The model requires that users and their devices be constantly evaluated.
2027? Really? In the time it took to fight WW2? That is how long it will take?
Sigh.
DOD security should be at the leading edge, but it is simply - and almost criminally - not. This move is overdue - and not just for spying reasons. With everything quickly reaching the point that if for any reason the military is locked out of its computer systems, a lot of what it takes to keep the front lines fed, fueled, and informed comes to a screeching halt. The threat isn’t just spying through a poorly designed security construct - but denial of access to your IT infrastructure with malware. You need to stop your good stuff from leaking out, and their bad stuff sneaking in.
A bit of malicious code can be just as effective as a few tons of TNT.
Need some more help with “Zero Trust?” For the details, I think this Crowdstrike article is a good start;
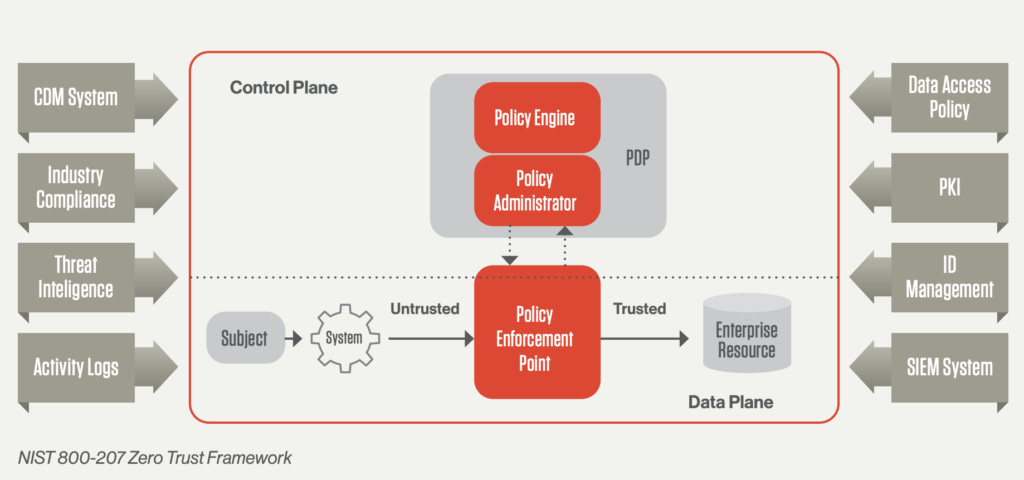
The Zero Trust model (based on NIST 800-207) includes the following core principles:
Continuous verification. Always verify access, all the time, for all resources.
Limit the “blast radius.” Minimize impact if an external or insider breach occurs.
Automate context collection and response. Incorporate behavioral data and get context from the entire IT stack (identity, endpoint, workload, etc..) for the most accurate
As spring comes to an end, I’m curious how this worked out;
Hackers backed by the U.S. Department of Defense will attack networks run by Amazon, Google, Microsoft and Oracle to better understand zero-trust cybersecurity in commercial cloud environments.
So-called red teams of ethical hackers from the National Security Agency will test the digital strength of the four cloud service providers, or CSPs, starting in the spring. The Defense Department in December selected the companies for its $9 billion Joint Warfighting Cloud Capability, a follow-up to the failed $10 billion Joint Enterprise Defense Infrastructure arrangement.
“We’re going to have the NSA red team, and perhaps even service red teams, attack,” Zero Trust Portfolio Management Office Director Randy Resnick said at a Jan. 19 event hosted by Billington Cybersecurity. “That would be a realistic adversary attack, a controlled attack, and we would determine whether or not the red teams could get and exploit data.”
The operation — of mutual agreement and not a requirement tied to the JWCC deal — will inform how the Defense Department proceeds with zero trust. It could also prove the vigor of the cloud providers and lay the foundation for future zero-trust-enabled storage and computing.
One thing that keeps coming to mind here is 2027.
DOD is behind on security. It is a critical issue almost at crisis level. Those at the front have clearly identified it as such, yet “the system” says they will resolve it in a period of time slightly more than a WorldWar.
Where is the urgency? It appears, again, that the process is the product.



It's been apparent to me after holding a TS clearance for more than 52 years with SCI access for half that, is that beyond the IT focus that you are speaking to, we have gotten away from the foundational concept of:
"NEED TO KNOW"
Maybe it was the post 9-11 drive to "tear down walls that prevented info sharing" or the whole "Jointness Uber Alles" mindset, but too many people collect too many tickets and badges for programs they have no earthly reason to need other than ego.
Bradley Manning, a PFC in A-stan had no reason to have access to classified Dept of State cables regarding eavesdropping on the German PM for example. Why some ANG E3 needed SCI info on Ukrainian 155mm stocks? is a 155mm hung on an F-35 now?
The whole mindset needs to be inverted.
Need to know is the basic reason for access.
9/11 has increased the need for moving info out of compartments, but maybe be should return to those prior tenets.
Like the sign at Intel School in San Diego said, "Intelligence, the worlds second oldest profession, with morals and standards just slightly better than the first".